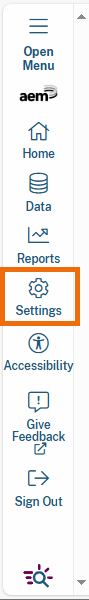
Settings Button in Navigation Menu
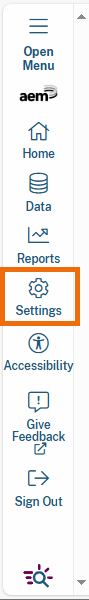
Settings Button in Navigation Menu
.png?alt=media&token=eae3ad84-34e3-40c5-8f42-b66551fe4437)
Settings Page
| Data Sources | Learn how to connect to a database. | data-sources |
| Data Suppression | Learn how to define your suppression rules. | data-suppression |
| Footer Links | Learn how to customize footer content. | footer-links |
| Language Translation Options | Learn how to set language translations for reports. | language-translation-options |
| Security | Learn how to configure security settings. | security |
| User Management | Learn how to manage user roles and permissions. | user-management |